I’ve been on a cloud kick lately. In the past year, I’ve passed my AWS CCP, Azure Fundamentals, and CCSP certifications. I’m currently studying for my AWS SysOps Associate, and realized I’m not finding a lot of information breaking down AWS from a networking perspective.
In today’s blog, I wanted to share a video I just made on the fundamentals of AWS networking and specifically explaining it from a network engineer’s perspective. In the video we covered AWS Regions, AWS Availability Zones (AZ’s), AWS Virtual Private Clouds (VPC’s), AWS Subnets, AWS Routing Tables, AWS Network ACL’s (NACL’s), Elastic IP’s, AWS Internet Gateways (IGW’s), and AWS NAT Gateways. We discuss not only what they are, but how they support each other, and we even built out a test environment using the AWS VPC Wizard including all of the networking components discussed.
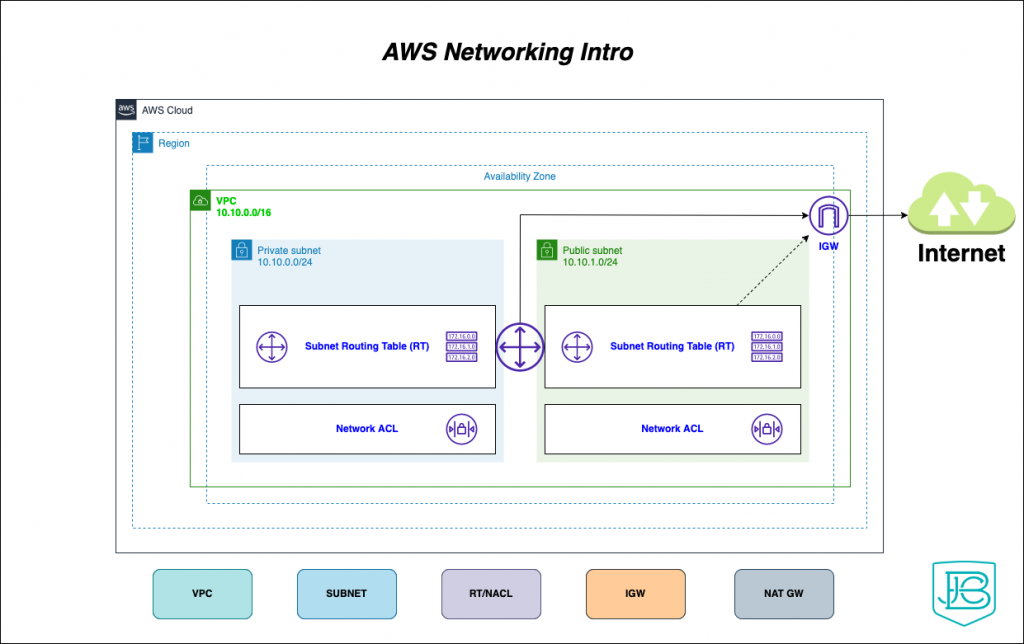
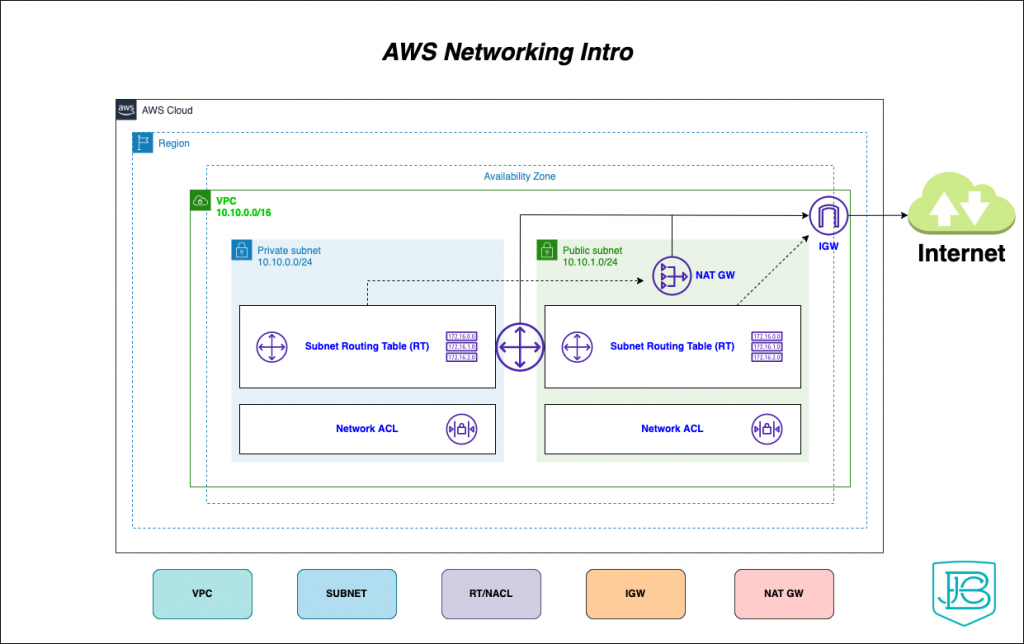
In making the above video I wanted to also create a diagram that fully covered all the different components and showed how they overlay on each other. Below are the diagrams and some high level summary points!
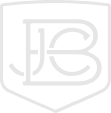
AWS Cloud, Regions, and VPC’s
- The AWS cloud is made up of different regions that are all across the world
- Regions have a different amount of AV’s which are made up of a collection geographically close data centers
- Customers create a VPC that can span multiple AV’s but has to remain within an individual region (VPC’s can communicate with each other, but that is a more advanced networking topic for later).
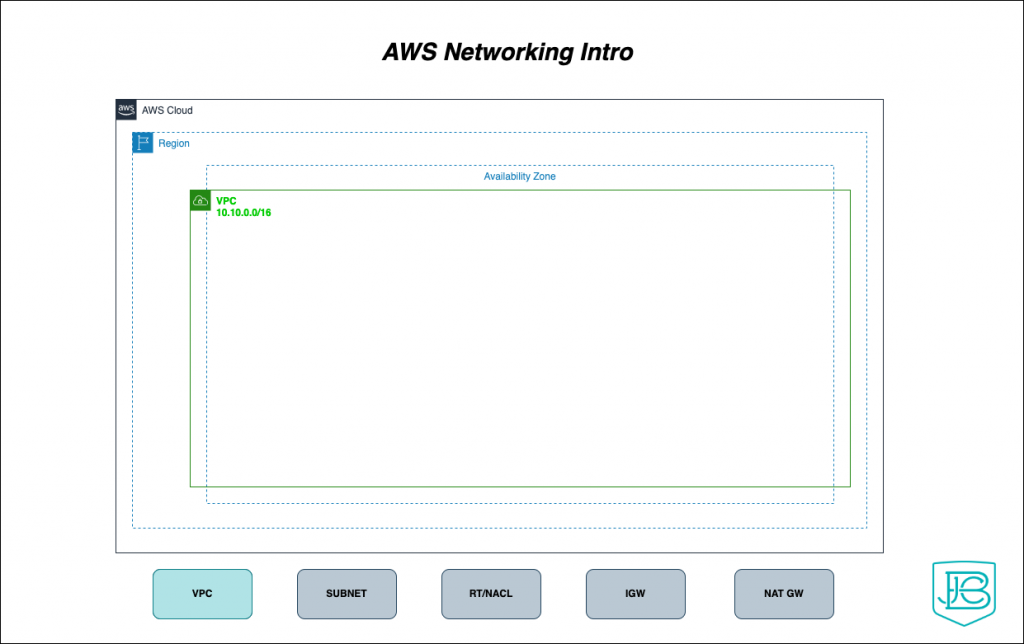
AWS Subnets (Public and Private)
- Within a VPC you have different types of subnets: public and private
- A subnet resides within an AV, but can talk to other subnets within the VPC independent of AV
- Private subnets could have access outbound the Internet (via a NAT GW) but the Internet doesn’t have access to it
- Public subnets have access the internet and the internet can access it (via a IGW)
- In both cases, the IP space is probably RFC 1918 space (10.0.0.0/8, 192.168.0.0/16, 172.16.0.0/12)
- Routable IP space can be used, but not advertised by AWS (this is an on-prem/hybrid advanced networking topic)
- In order to get AWS publicly routable space associated with hosts in the subnets, you’re going to need to use an Elastic IP address
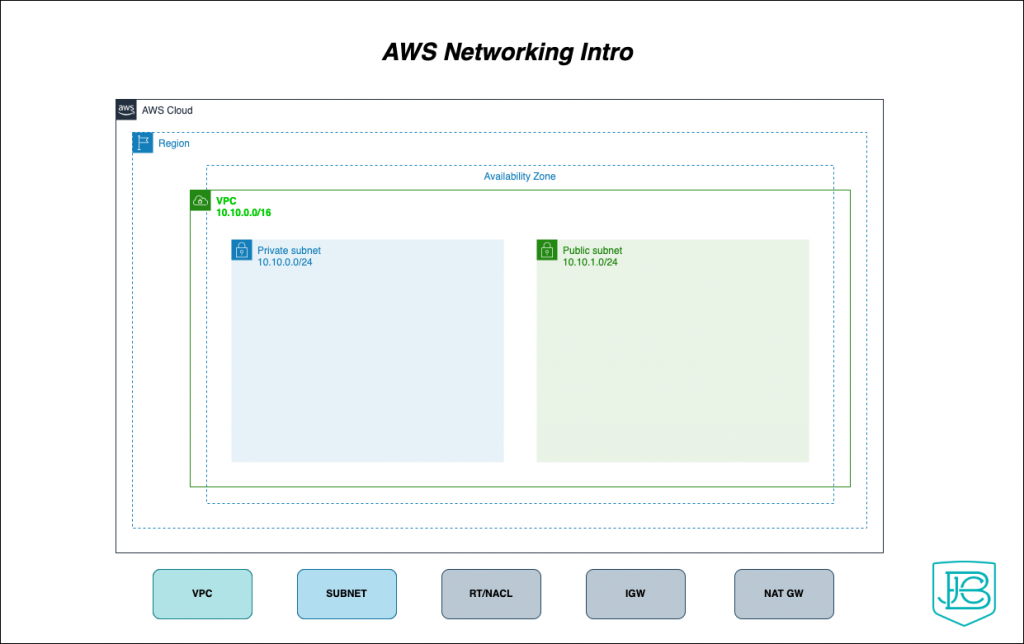
AWS Routing Table and Network Access Control Lists (NACL’s)
- Each subnet needs to have a routing table
- Multiple subnets could share same route table, but private and public subnets should have their own route tables
- Routing is able to take place between the private and public subnets due to the AWS routing infrastructure
- Each route table has a local route for the VPC’s subnet, in the above case, 10.10.0.0/16
- The Network ACL is a non-stateful access control list that can be applied to a subnet or subnets, think of it like an ACL on a switch
- The ACL must allow the return communication, as it is not stateful
- There are stateful ACL’s called Security Groups which are applied to individual instances/IP’s
AWS Internet Gateway (IGW)
- The IGW resides in the public subnet and the routing table associated with the public subnet has a default route to the IGW
- The IGW doesn’t reside within a AV, but within the overall VPC
- The IGW does a NAT translation of public subnet IP’s to the Elastic IP addresses that are assigned to each virtual instance interface (such as an EC2 server instance)
AWS NAT Gateway
- The NAT Gateway resides in the public subnet
- The routing table for the private subnet has a default route that points to the NAT Gateway
- The NAT Gateway has an Elastic IP associated with it, all internal private subnet traffic going to the internet will be sourced from this IP
Make sure to check out the video at the top as well, where I go a bit more in depth, and even show how we can build all of this infrastructure out in under 5 minutes!
Network Knowledge Wrap Up
A great resource on learning AWS networking, is the AWS Networking Fundamentals book (Affiliate Code)